The RADIUS adapter allows Itential Platform to interact with a RADIUS server for authentication. Use this procedure to configure RADIUS-based authentication.
The RADIUS server must include a vendor-specific attribute (VSA), typically placed in the dictionary file. The syntax provided in Configure FreeRADIUS files corresponds with this guide and applies to FreeRADIUS. The syntax for other RADIUS servers may differ — refer to your RADIUS server’s documentation for the exact syntax required. You must also ensure users and groups are correctly configured with the Itential-Group VSA attribute.
The following steps provide a basic installation process using FreeRADIUS as an example. IPs, usernames, groups, and passwords will vary with your environment. This sample installation was performed on a CentOS 7 virtual machine in a test environment.
These instructions are provided as an example — your environment will differ.
A vendor-specific attribute (VSA) is required when using FreeRADIUS. Add the VSA information to the dictionary and users files. The RADIUS configuration file at /usr/lib/firewalld/services/radius.xml will most likely not require changes.
After logging in to Itential Platform, select Admin Essentials in the left navigation menu.
Click the plus sign in the top toolbar to create a new adapter. The Create dialog opens. Click the dropdown arrow and select Adapter from the menu list.
Enter a name for the adapter (for example, Local_RADIUS) and select the RADIUS adapter type from the dropdown menu.
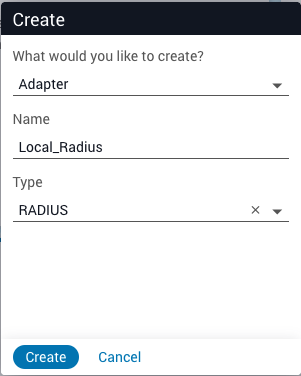
Click Create. The adapter appears in the Adapters collection menu on the left and the Configuration tab displays automatically.
The configuration below shows the default parameters. You must include the correct groups that will be allowed to access Itential Platform — at a minimum, include the group that will have administrative rights. If a login user and their associated group are not listed, they will not have access to any adapters or apps within Itential Platform.
If you use a name other than Local_Radius, update the "id" property along with the "name" and "group" properties under "radius_groups".
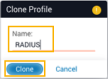
Select an existing profile (usually profile1) from the Profiles collection in the left navbar. Click the stacked dots icon in the upper-right and select Clone from the menu options.

Enter a name for the new profile (for example, RADIUS) and click Clone. The profile appears in the Profiles collection on the left and the Configure editor displays.
To encrypt the secret under the adapter properties, refer to Password Encryption.
If you encounter issues using the RADIUS adapter:
If you cannot access Itential Platform using the RADIUS profile, revert to the original profile. From a terminal prompt, use root login to edit /opt/pronghorn/current/properties.json and set the active profile to profile1:
Restart the Itential Platform service and attempt to log in again:
If problems persist, the issue is usually related to configuration. Check the following:
RADIUS adapter:
kill command and the PID for the RADIUS adapter.RADIUS server:
/etc/raddb/clients.conf./etc/raddb/users./etc/raddb/dictionary.See the FreeRADIUS documentation for further instructions on installation, configuration, and troubleshooting.