The following diagram shows the authentication flow in Itential Platform using LDAP.
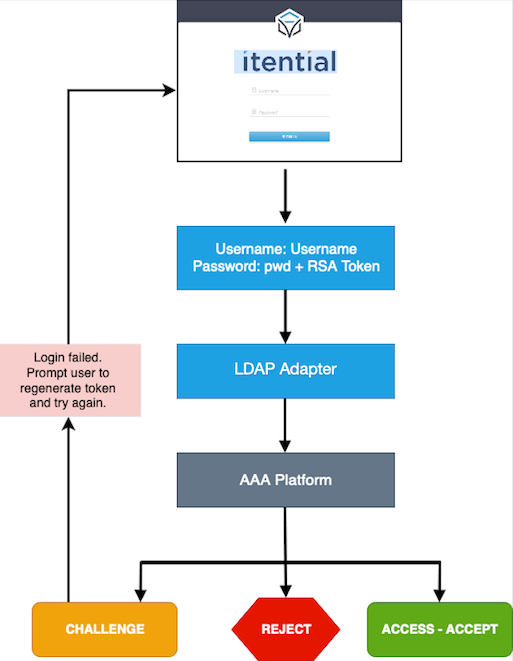
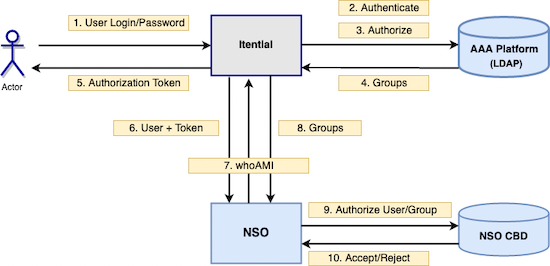
Reject — Itential Platform displays “Invalid credentials.”Access-Accept — Itential Platform allows user to log in.Challenge — Itential Platform displays “Generate token and retry.”47688 (Itential)Itential-user-Group1The following diagram illustrates both authorization and authentication between Itential Platform and NSO using LDAP.
The following applies when using multi-tenancy:
whoami API request to Itential Platform.Multi-tenancy is not required for most implementations.