The NSO adapter connects to NSO using the web UI port and NETCONF port. Each time the NSO adapter establishes a connection to NSO, the adapter reads the service models advertised by NSO. To securely configure the NSO adapter, ensure the HTTP hostname is configured with the same hostname in the common name of the NSO server certificate.
See Cisco NSO Service Manager for more information.
Configure at minimum the following properties before deploying:
http.hosthttp.portssl.enabledssl.caFilessl.ciphersnetconf.hostnetconf.portcredentials.usercredentials.passwdThe default configuration uses machineLogin for all transactions. To enable individual user authorization handled by NSO, NSO must be configured with an external authentication script capable of returning external group memberships for a given user ID. Ensure NSO is configured for external authentication and set authenticationStrategy.method to tokenLogin.
To support various versions of Cisco NSO, Itential offers two packages: itential-tools and itential-tools-nso6.4.
If you have access to the itential_tools repository in Nexus, you can access both packages and choose which to install based on your NSO version.
itential-tools is compatible with NSO versions: 5.6.x, 5.7.x (LTS), 5.8.x, 6.0.x, 6.1.x (LTS), 6.2.x, and 6.3.x.
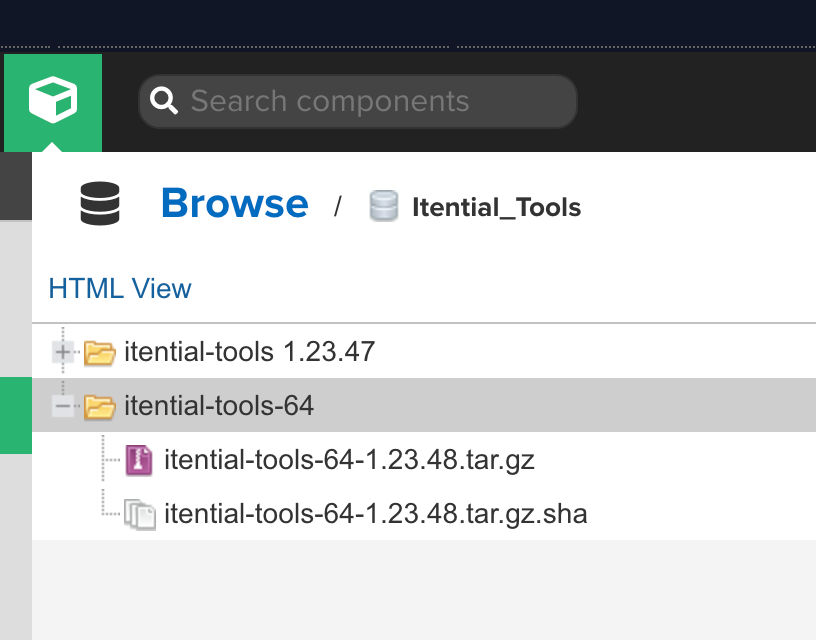
itential-tools-nso6.4 is built specifically to support NSO 6.4 and above.
If you are using NSO 6.4 and above with itential-tools-nso6.4, you must use one of the following minimum versions of adapter-nso:
The Nexus repository contains two folder types: itential_tools and itential_tools-64. Each folder contains the assets and components necessary for Itential Platform to interact with NSO.
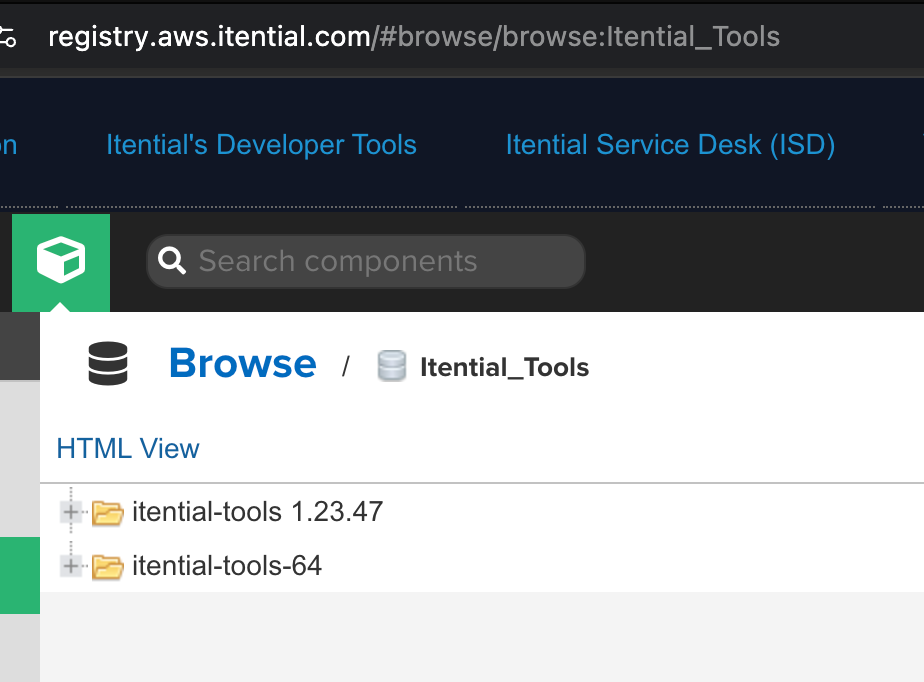
itential-tools 1.23.x supports Cisco NSO 5.6.x, 5.7.x (LTS), 5.8.x, 6.0.x, 6.1.x (LTS), 6.2.x, and 6.3.x.
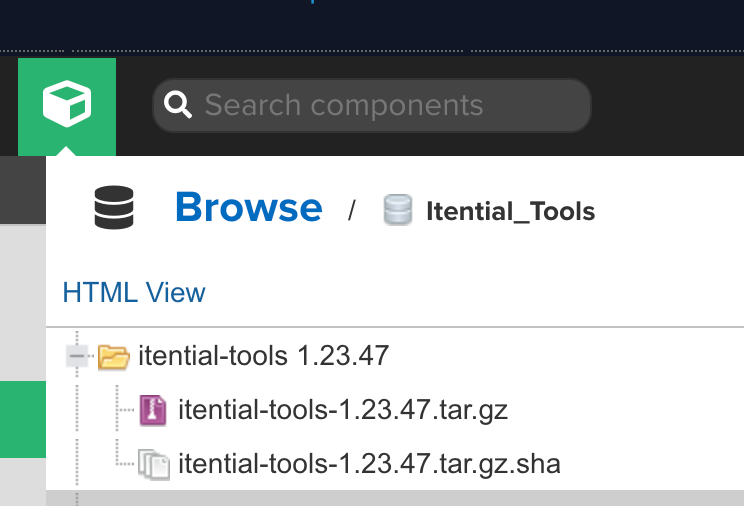
itential-tools-64 supports Cisco NSO 6.4.x and above, and contains itential-tools-64-1.23.48 as the first package release.
To use external authentication, install the ph-auth script and configure the ncs.conf file. The NSO external authentication script requires Python and the requests module.
Network connectivity is required between NSO and Itential Platform (typically port 3000).
Configure the ncs.conf file to use external authentication. Both external-authentication and either local-authentication or PAM should be enabled. Itential Platform initially connects using a global service account with admin privileges.
When performing transactions that can bind a request to a human user account, Itential Platform makes calls on behalf of a specific user (for example, bobjones instead of admin).
Restart NSO:
If the tokenLogin feature of the NSO adapter will be used, verify that users properly map to the appropriate southbound credentials. Ensure credentials are configured for the default umap inside NSO. Run this command for each authentication group, applying the appropriate device credentials as remote-name and remote-password:
To use Itential Platform with an NSO NETCONF Access Control Model (NACM) implementation, reference the sample set of NACM rules provided with this package.
The NACM rules assume the following groups model:
These groups are shared across both Itential Platform and NSO. Using the sample external authentication script, Itential Platform provides the set of groups defined inside Itential Platform and discovered from the configured AAA system to NSO, to be applied to the NACM rule-lists.
The set of groups returned by the NSO AAA provider must properly match NACM rule-list group assignments.
The following rule-lists are provided in the sample rules:
Adjust the groups associated with these rule-lists to ensure they are mapped to the correct user accounts.
Load sample-nacm-rules.xml into the NSO CDB using the load merge feature of ncs_cli:
The sample NACM rules contain a rule-list for whitelisting devices to the users group. Configure the sample rule-list or create your own to associate devices with groups of users:
In a NACM-enabled system, any new device added must have its groups defined at the time of device turn-up. This applies to both manual configuration in NSO and device turn-up workflows.
The sample NACM rules contain a rule-list for whitelisting service instances to the users group. Add all service instances for a model to the users whitelist:
To add a single instance instead:
In a NACM-enabled system, any new service instance added must have its groups defined. Service instances may be restricted to an individual group or made accessible to multiple groups with the appropriate NACM rules.
Configure workflows in Itential Platform to wait for Cisco NSO northbound NETCONF event notifications before proceeding.
Cisco NSO emits notifications over NETCONF for various events. The NSO adapter can be configured to listen to NSO NETCONF event streams, and the Itential Platform Event System can consume and process these events within a workflow.
Event streams are configured in NSO within the ncs.conf file. NSO allows the following event streams:
ncs-alarmsncs-eventsdevice-notificationsservice-state-changesNETCONFThis example configures an ncs-alarms event stream inside ncs.conf:
Every stream that is configured must be defined within ncs.conf regardless of whether it supports replay. NSO logs notifications, and a NETCONF client can request logged notifications if replay support is enabled.
Define which NSO NETCONF event streams to subscribe to using the netconfSubscriptions property in the adapter properties. Restart the NSO adapter after updating the adapter properties. The netconfSubscriptions values should correspond to the desired NSO NETCONF streams defined in ncs.conf.
Example adapter-nso properties with netconfSubscriptions defined:
The Workflow Engine eventListener task is used to listen for events from applications and adapters deployed inside the platform.
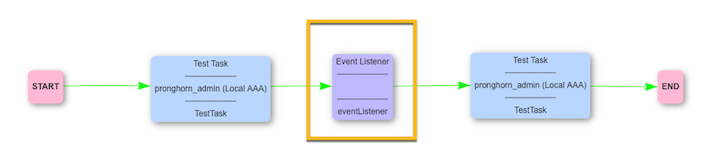
Refer to the eventListenerJob task reference for more information.
When a job is created, it processes all the tasks it can. Upon reaching the eventListener task, the job waits in a running state until it receives an event. The event it waits for is configured within the task itself.
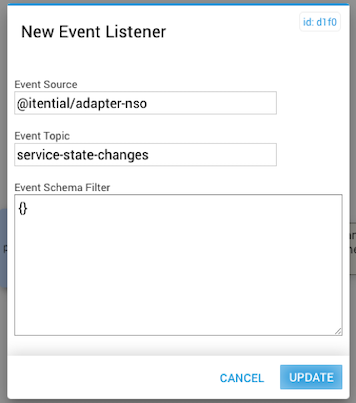
This example processes the eventListener task only when the following payload is received:
The JSON schema for the Event Schema Filter:
If you do not need to filter on the payload and only want the task to execute when it receives a specific Event Topic, set an empty JSON object {} in the Event Schema Filter field.
The Itential Tools Rules Engine allows users to define scripts that execute prior to NSO command-sets being run. These scripts modify (add or change) values in the NSO command-sets before execution.
The rules engine has two parts: a rule engine and a script engine. The script engine reads the script files defined for the command that is passed in, reads in the defined rules, then passes the rules to the rule engine for processing.
The following files are required:
The main framework for the Java-based application is the Java Spring framework.
The Itential Tools Rules Engine has three functional areas: Script Engine, Rule Engine, and Script Validation Engine.
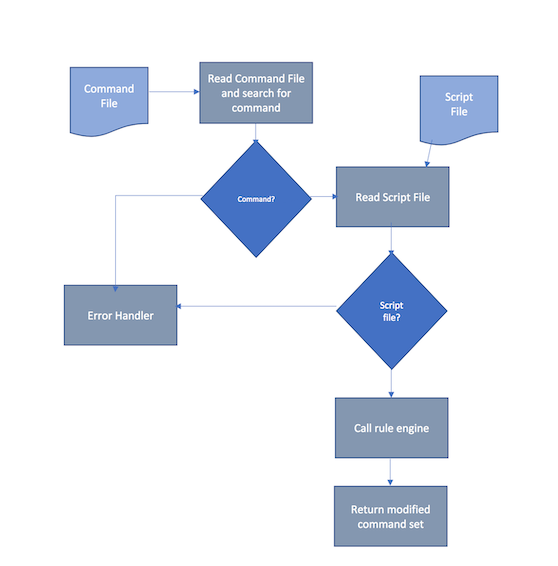
Script Engine — The main driver for script processing. It receives the command file containing the request to modify the NSO command-set, locates the command to get the script file to execute, reads in the script file, calls the rule engine to process the rules, modifies the NSO command-set appropriately, and returns the modified command-set. Errors are handled and returned to the calling system.
Rule Engine — Responsible for processing each rule. Input parameters are the rule and the NSO command-set. Output is the modified NSO command-set. Steps: receive parameters, determine which rule to process, perform the rule process and modify the command-set, return the modified command-set, and handle errors by passing them back to the Script Engine.
Script Validation Engine — Validates that the script has the correct format and that commands are valid with the correct number of parameters. If any validation fails, a custom Java exception is thrown with the appropriate error message and code.
$DLC_REPLACE — Four parameters: 1st (Any String), 2nd (Any String), 3rd (Int), 4th (Int).
$DLC_INSERT — Five parameters: 1st (Any String), 2nd (Any String), 3rd (Before or After), 4th (Int), 5th (Int).
$STRING
Syntax: $STRING['my string'|'2nd string'|'3rd string']
A single value or an array of strings separated by a pipe (|) that will be printed out. An array causes a loop.
$LOOP
Syntax: $LOOP[{start}-{end}|$STRING['{string to print out}']$LOOP_VAR]
Parameters: {start} (starting int), {end} (ending int), {string to print out} (any string), $LOOP_VAR (the current loop iteration integer). Multiple references to $LOOP_VAR are supported.
Example:
Implementation of the Rules Engine includes: integration into the current itential-tools Java application, a mechanism to refresh the command list without restarting itential-tools, an option to bypass the refresh, and the ability for users to update commands and scripts.
Rule Engine integration — Include the Java jar file generated by the Rule Engine application in the private-jar or shared-jar directory to build the itential-tools application. Import the com.itential.datalore_utils.ScriptEngine package into the calling class:
Update your desired NSO adapter under Settings > Services > Adapters with the following configuration:
To identify the preferred cipher for your SSL handshake, run the following command from the Itential Platform server:
In the example output below, the preferred cipher is ECDHE-RSA-AES128-GCM-SHA256:
The following principles apply to the NSO adapter in an LSA architecture:
For the following LSA architecture — an “upper” NSO service with service models defined, and one or more “lower” NSO services connected to devices — set up Itential Platform as follows:
adapter-nso instance and point it to the upper node.adapter-nso instance for every lower node.With this setup, you can use service models (for example, with tasks such as saveInstances) and perform device management (for example, with Configuration Manager).
NSO can also utilize an Itential Platform broker to further support this setup. When an app task like saveInstances is used, you provide the device name to the task. The Itential Platform broker queries all adapter-nso instances to see which one has that service model and uses that adapter instance. The same principle applies to tasks that directly interact with devices — for example, the golden config feature in Configuration Manager uses a broker to determine which adapter-nso instances manage which device.